Calterah Cybersecurity White Paper Ⅵ: Calterah CalShield™—Automotive Radar Security Solution
2026-01-21
In the first white paper on Calterah Vehicle Security Subsystem Solution for Radar, we provided an overview of the architecture, risks, and challenges of automotive radar security and Calterah’s fundamental cybersecurity capabilities. This white paper focuses on the specific implementation of security mechanisms and core protection technologies, offering an in-depth analysis of how the Calterah CalShield™ solution transforms theoretical security strategies into robust and verifiable chip-level capabilities, ensuring full-link security for intelligent automotive radar systems, covering all stages from boot-up and operation to data storage.
1 Automotive Cybersecurity Trends
As the automotive industry’s requirements for the precision of automotive radar devices evolve, the algorithms and systems behind them are becoming increasingly complex, leading to a rising demand for resources, such as storage. This, in turn, significantly broadens the potential attack surface of radar compared to that of other devices.
2 Secure Storage via External Flash
As the algorithms and systems of radar devices become increasingly complex, the demand for storage space for both data and programs continues to grow. As a result, external flash memory has become a common option for radar devices, typically used to store the following:
- System Images
Given the large size of a device’s system images, they are usually stored in an external flash device, which makes them liable to be extracted for reverse engineering or tampering to bypass system restrictions. - System Configuration Data
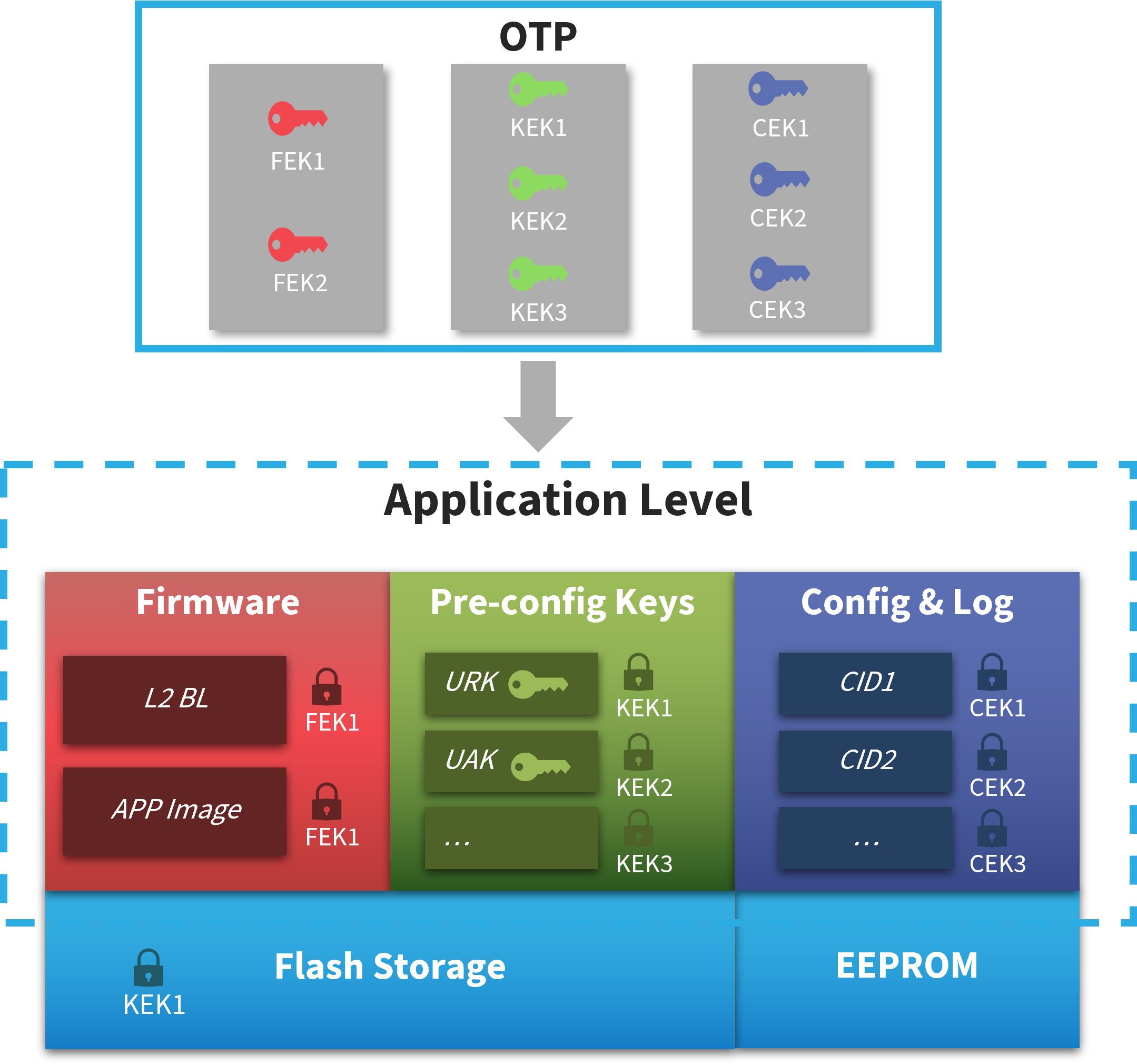
System configuration data, as inputs or outputs, tends to conceal sensitive information. Any unauthorized modification will likely lead to unpredictable consequences. - System Keys
System keys, as special data, are often the prime targets of cyberattacks. These keys may include user root keys, application keys, etc.
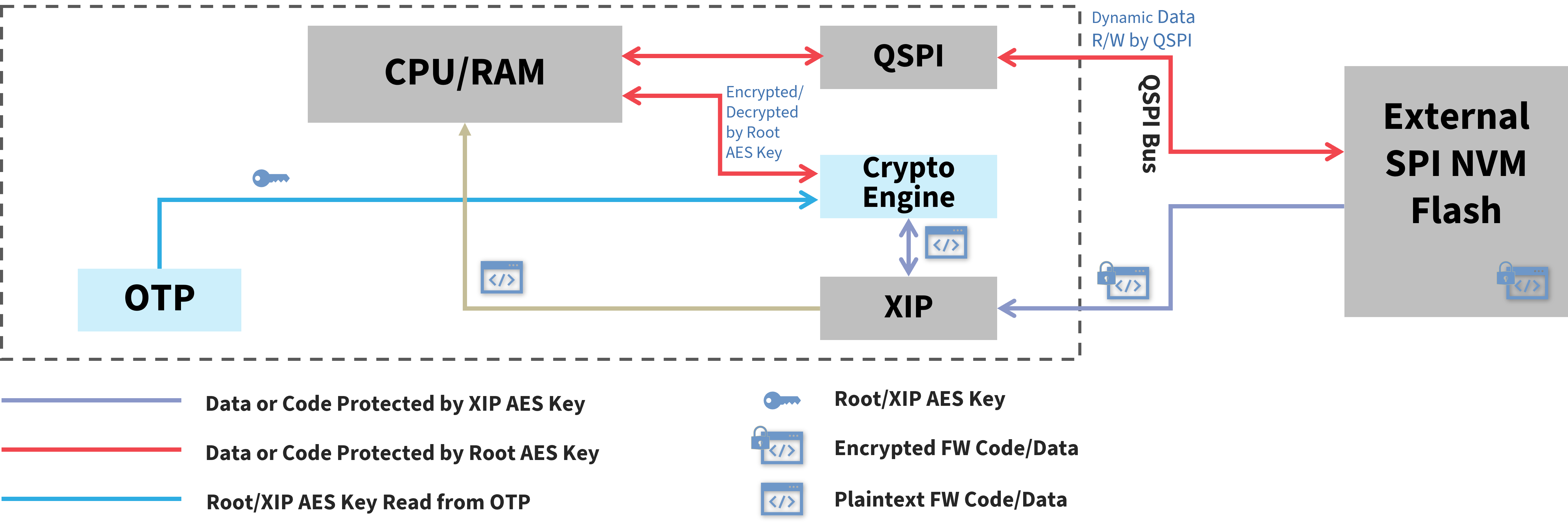
Therefore, multi-layered protection should be applied to external flash devices. Considering the complexity of system data, Calterah has designed differentiated protection solutions for different data types. Specifically, at the system level, Calterah provides a hardware encryption solution that enables high-speed storage protection. This solution can also work with the encryption measures tailored to different data types across various applications, forming a multi-layered protection system that significantly increases the difficulty for hackers to breach the system.
3 Secure Boot
Hackers often bypass system restrictions by tampering with the system images or by other means to control the system or access system data. Such cyberattacks may not only result in malicious or abnormal modifications of system functions, but can also lead to integrating unauthorized components or activating unauthorized functions. The Secure Boot mechanism can effectively prevent the system from executing tampered image files, which is gradually becoming a standard feature in the automotive industry, widely applied across various domains.
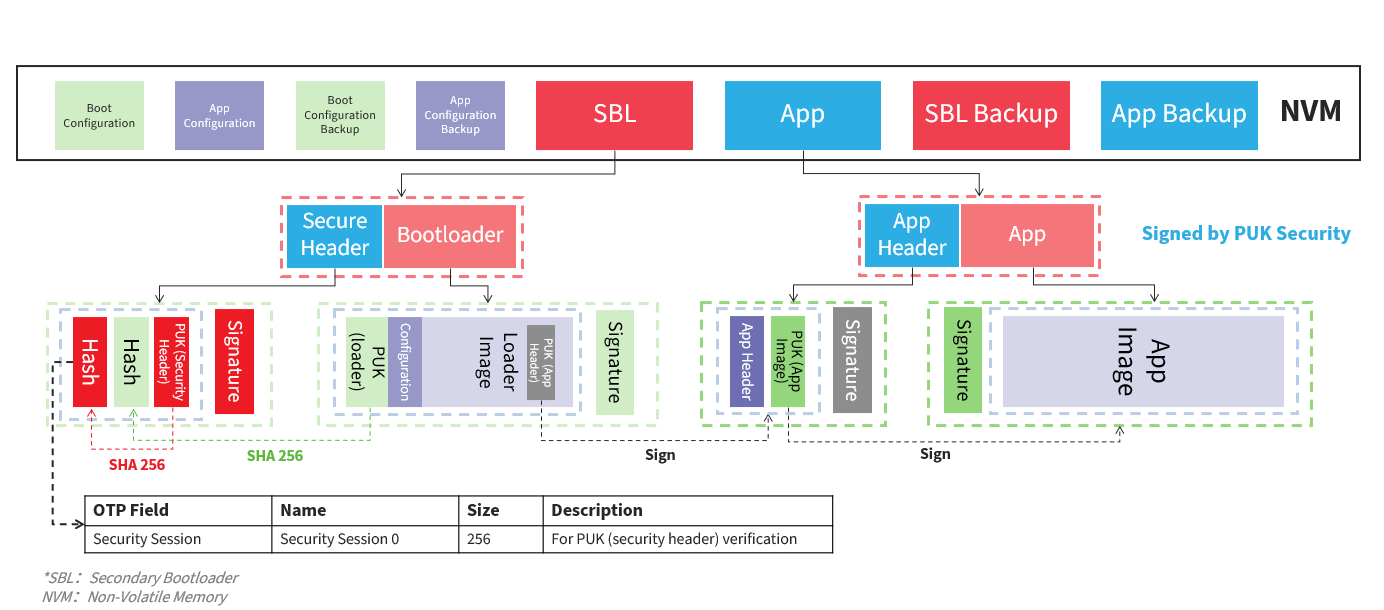
The multi-stage boot solution provided by Calterah supports multiple asymmetric algorithms, such as RSA, ECC, ED25519, SM2, etc. and the signature algorithm SHA2, which deliver robust protection for image integrity. The solution covers all components across the full boot chain from Bootloader to system images, and achieves end-to-end system-level verification, ensuring that malicious users cannot tamper with any part of the system.
4 Cryptographic Capabilities of CalShield™
Calterah’s automotive radar security subsystem, CalShield™, provides comprehensive cryptographic algorithms for both the system and higher-layer applications. CalShield™ is compatible with algorithms of different types and strengths as well as performance requirements, ensuring that it delivers corresponding cryptographic support for scenarios such as Secure Onboard Communication (SecOC), Secure Diagnostics, and Secure Update. Its wide range of algorithm portfolio and performance capabilities can fully meet all kinds of demands.
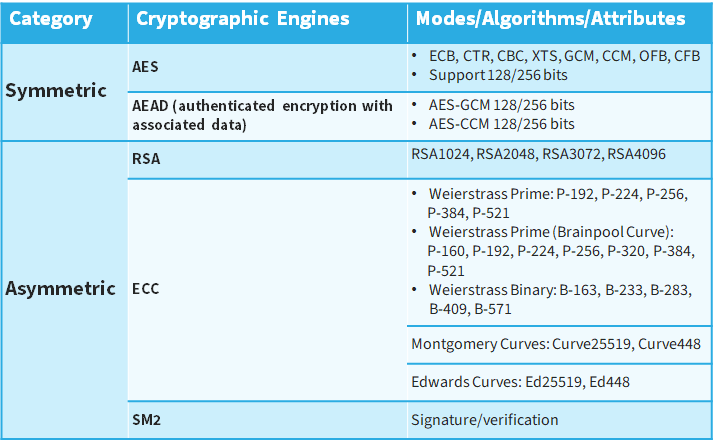
Regarding symmetric algorithms, Calterah supports the following:
- AES (Advanced Encryption Standard)
Supporting AES algorithms in various modes, such as ECB, CTR, CBC, XTS, GCM, CCM, OFB, and CFB, with a key length of 128 bits or 256 bits
*ECB: Electronic Codebook
CTR: Counter
CBC: Cipher Block Chaining
XTS: XEX encryption with tweak and ciphertext stealing (XEX: XOR-Encryption-XOR)
GCM: Galois/Counter Mode
CCM: Counter Mode with CBC-MAC
OFB: Output Feedback
CFB: Cipher Feedback - AEAD (Authenticated Encryption with Associated Data)
Supporting AES-GCM and AES-CCM modes with a key length of 128 bits and 256 bits
*GCM stands for Galois/Counter Mode, and CCM for Counter Mode with CBC-MAC.
Regarding asymmetric algorithms, Calterah supports the following:
- RSA Algorithms
Supporting 4 key lengths: RSA 1024, 2048, 3072, 4096 - ECC (Elliptic Curve Cryptography)
The following ECC algorithms are supported:
Weierstrass Prime: P-192, P-224, P-256, P-384, and P-521;
Weierstrass Binary: B-163, B-233, B-283, B-409, and B-571;
Weierstrass Prime (Brainpool Curves): BrainpoolP160r1, BrainpoolP192r1, BrainpoolP224r1, BrainpoolP256r1, BrainpoolP320r1, BrainpoolP384r1, BrainpoolP512r1;
Montgomery Curves: Curve25519 and Curve448;
Edwards Curves: Ed25519 and Ed448.
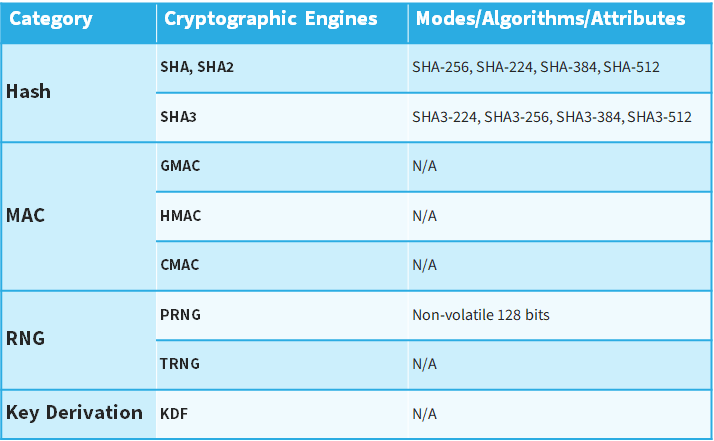
Regarding hash algorithms, Calterah supports the following:
- SHA/SHA2
Supporting SHA-224, SHA-256, SHA-384, and SHA-512 - SHA3
Supporting SHA3-224, SHA3-256, SHA3-384, and SHA3-512
Calterah also supports China’s cryptographic algorithms specifically required in the industry, including SM2, SM3, SM4, SM9, etc., in line with the trends and requirements of algorithm localization.
Besides, Calterah also supports the following different algorithms:
- MAC (Message Authentication Code)
Including various types of MAC algorithms such as CMAC, HMAC, and GMAC - RNG (Random Number Generator)
Including 128-bit Pseudorandom Number Generator (PRNG) and True Random Number Generator (TRNG) - Key Derivation
Supporting the key derivation function (KDF) algorithm
5 Conclusion
Calterah has enhanced performance designs of algorithms for encryption, signature, and signature verification, ensuring that the radar system can handle performance demands across diverse scenarios, including Secure Boot, Secure Update, Secure Onboard Communication, and Secure Diagnostics.
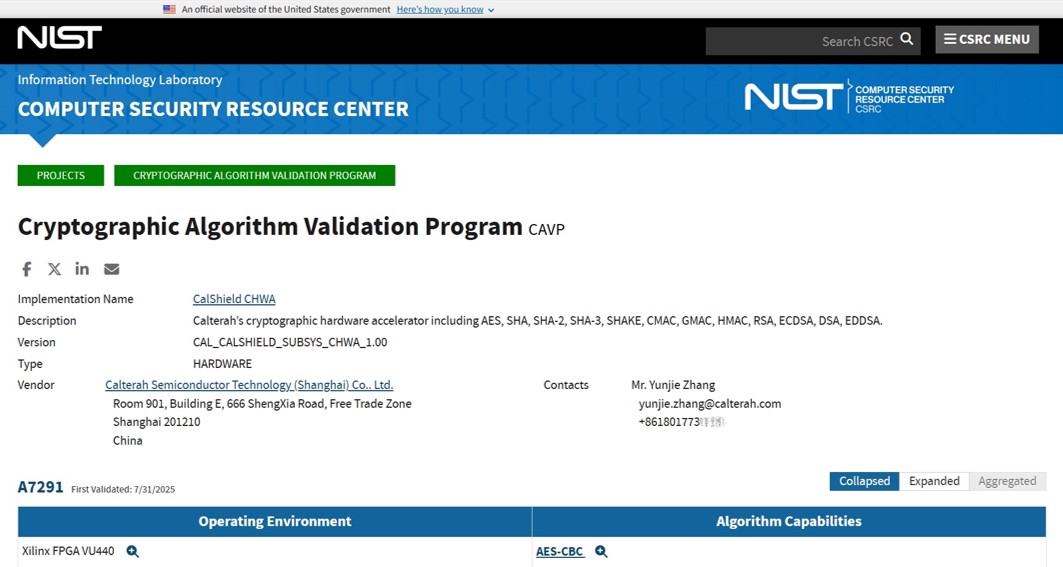
Additionally, Calterah’s security subsystem IP, CalShield™, has attained the certification of NIST FIPS CAVP*, guaranteeing that Calterah radar chips have integrated accurate and reliable cryptographic engines such as AES, Hash, and PKC, to provide strong support for various application scenarios.
*NIST stands for National Institute of Standards and Technology, FIPS stands for Federal Information Processing Standards, and CAVP stands for Cryptographic Algorithm Validation Program.
In terms of the overall design, Calterah has been continuously optimizing the security architecture for radar to ensure swift adaptation to the sharply changing automotive market, thereby providing users with robust and sustainable security protection.



.jpg)
.jpg)
.jpg)
